Using Digital Cookbook App in Smartphone for Cooking Stock Image - Image of cooking, electronic: 131084525
GitHub - PacktPublishing/Mobile-Device-Exploitation-Cookbook: Mobile Device Exploitation Cookbook by Packt Publishing
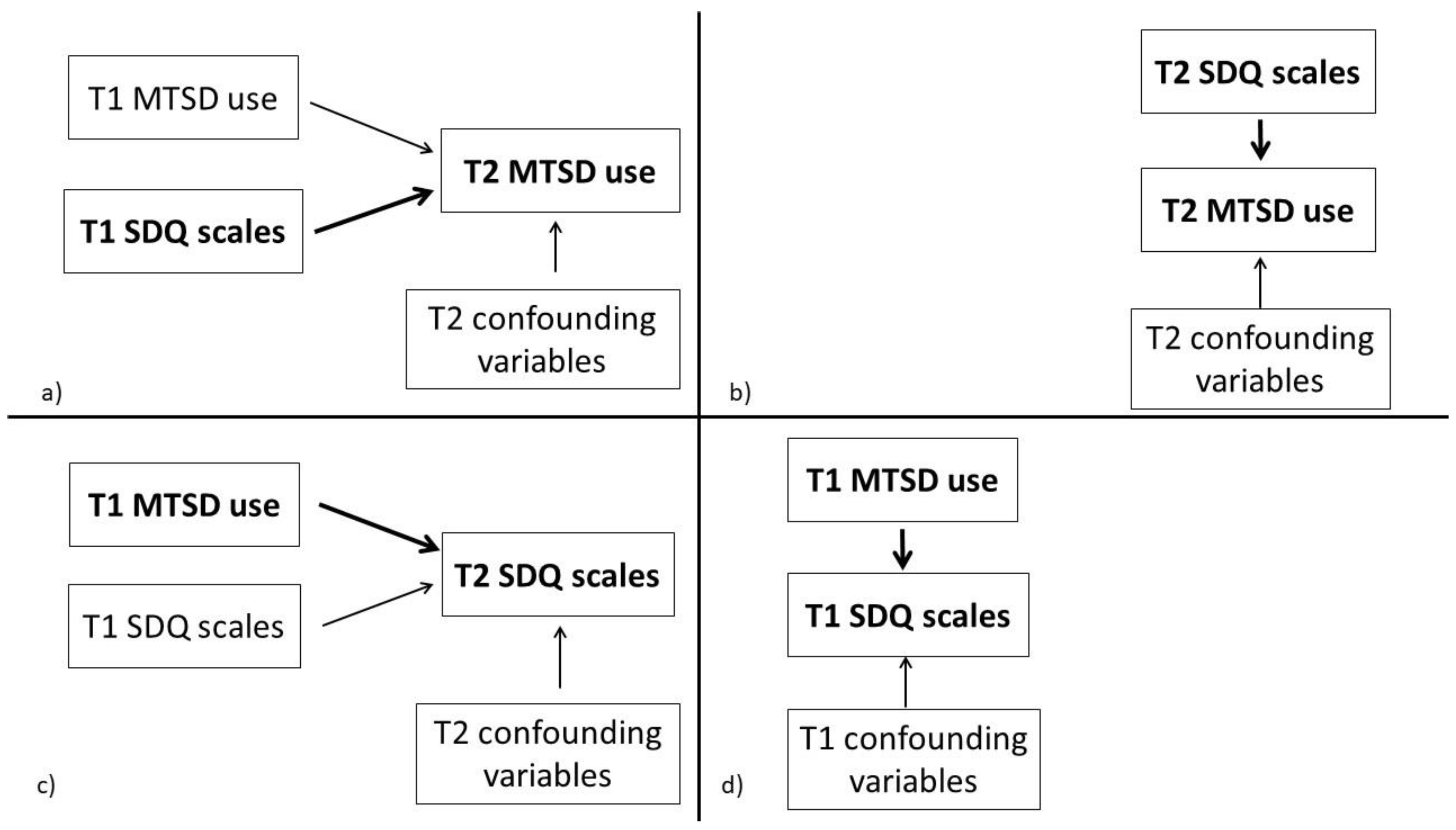
Sustainability | Free Full-Text | Longitudinal Associations of Children’s Hyperactivity/Inattention, Peer Relationship Problems and Mobile Device Use

Hands-On Application Penetration Testing with Burp Suite eBook by Carlos A. Lozano - EPUB | Rakuten Kobo United States

![PDF] Android Security Cookbook by Keith Makan eBook | Perlego PDF] Android Security Cookbook by Keith Makan eBook | Perlego](https://www.perlego.com/books/RM_Books/packt_pub_vpnckweg/9781782167167.jpg)